
Dunnottar Castle sits high on the cliffs near Stonehaven in Aberdeenshire. It’s scenic and sprawling and, though peaceful now, it boasts a turbulent history.

History of Dunnottar Castle
Dunnottar was attacked by Vikings in the ninth century, and captured by William Wallace in 1297. Kings and queens loved to visit: Mary Queen of Scots, James VI, and at one point during my own visit, I was standing in the bedroom of Charles II.

Ghosts!
Though I didn’t meet them, there’s said to be a lassie in a green plaid searching for her lost Pictish children, a young deer hound, and a Scandinavian military gentleman who likes to stare out to sea.
I understand the need to stare across the ocean. The seascape at Dunnottar is mesmerising.

The elevated position of the castle means you can see across miles and miles of silvery sea. The window below is located in the Whigs’ Vault that held imprisoned Covenanters in 1685. It’s a dark and terrible place. I had to reach out to the air and the sky and the light.

Views, views, everywhere…

But it’s time to go. It’s time to walk back up the many, many steps that seemed so inconsequential on the way down…

For more information on the wonderfully atmospheric Dunnottar Castle visit the official site.
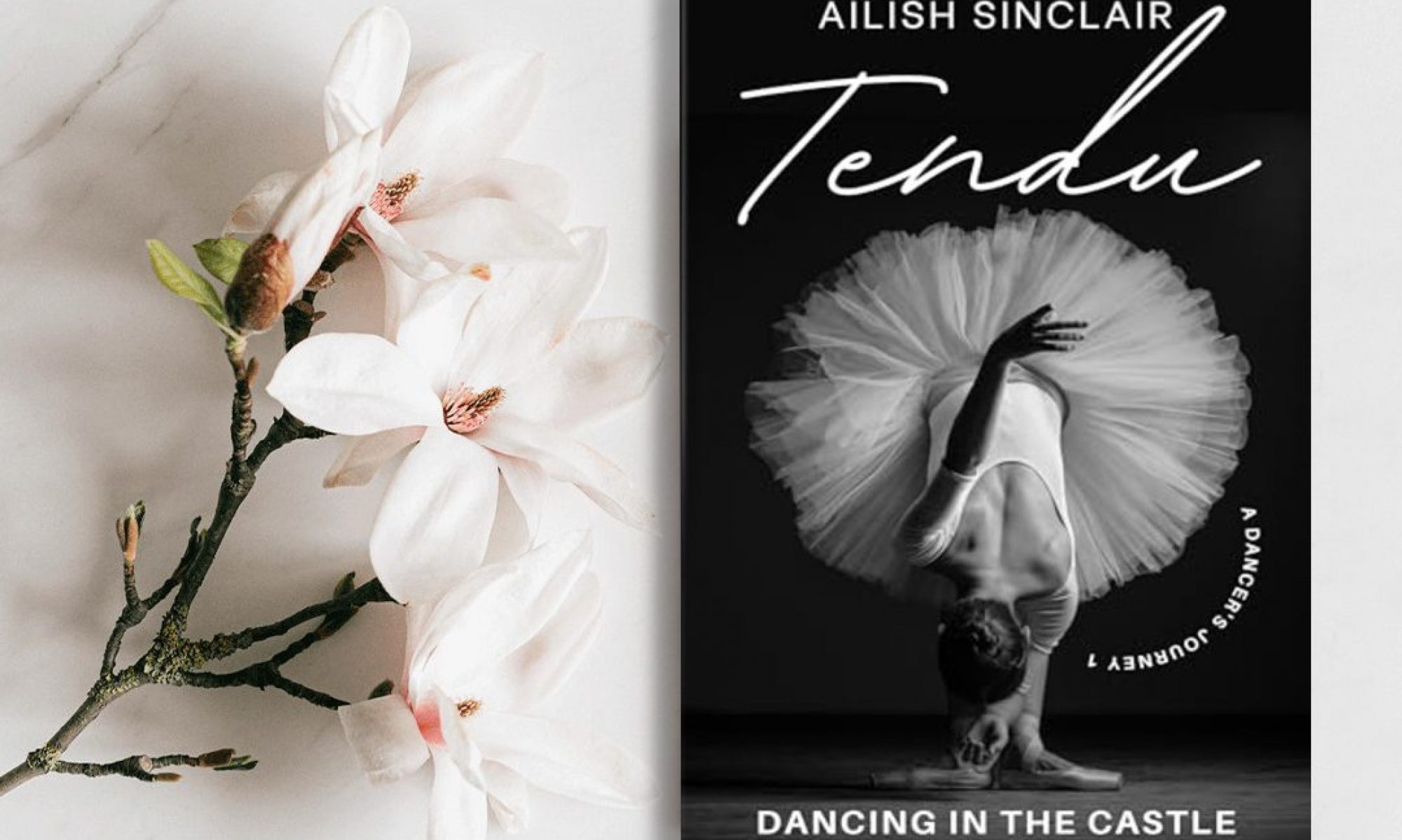
My Historical Novels

Set in 1st century Scotland, SISTERS AT THE EDGE OF THE WORLD includes the battle of Mons Graupius between the Romans and the Caledonian tribes. The book features a neurodivergent main character and some rather complicated romance!
“Ethereal and spellbinding…” Historical Novel Society
See the press release here
Read the article Roman Aberdeenshire features in author’s new book from Grampian Online.

Taking place mainly in a fictional castle, THE MERMAID AND THE BEAR blends an often overlooked period of history, the Scottish witchcraft accusations, in particular the 1597 Aberdeen witchcraft panic, with a love story.
See the press release here
From the Press and Journal: New book by Fraserburgh author highlights horrific extent of witch trials in Scotland

FIREFLIES AND CHOCOLATE was inspired by the kidnapped children and young people of Aberdeen. The story follows the adventures of Elizabeth Manteith from the castle and her determined efforts to get back home. There’s love. There’s derring-dos on the high seas… And there’s chocolate!
See the publisher’s Press Release here
“Filled with excitement and suspense…” Historical Novel Society
Newsletter and Free Story
You will receive a free short story when you sign up for my occasional, more-intimate-than-the-blog newsletter (the story can be read in a browser too).
The Performance: sometimes going home for Christmas is just one huge performance…
When Ariel returns home from dance college, her mother expects her to perform the Dance of the Sugar Plum Fairy in a pink, sequined tutu in front of many, many party guests. Ariel adjusts the costume and choreography to expose dark truths about her life, but, as it turns out, this is not the biggest performance of the night…

New Books and Special Offers
If you would like to hear about new books and special offers, you can follow my Amazon author page.
About Page

See my About Page here
Writer’s Tip Jar
Discover more from Ailish Sinclair
Subscribe to get the latest posts sent to your email.
Wonderful! 🙂
🙂
Wonderful place ,it was one of our favourite places we saw on our trip last year ,a must if one visits Scotland .
It is iconic, isn’t it?
What a wonderfully inspiring place. I can almost hear the voices of the past echoing from the stones!
It is an evocative site.
Great views!
They really were 🙂
What an amazing place. I and my wife (who has never visited the east of Scotland) had the intention this summer to visit some of the places you have described so enticingly but unfortunately one of my ‘health episodes’ intervened. Maybe next year.
I hope you’re better soon.
Thank you Ailish. Unfortunately the October break (my wife is a teacher) is already booked – anniversary – but here’s hoping for next year.
🙂
❤️
Thank you for this. It is such an amazing place…was there often as a child. The history is amazing too. Fabulous post.
Glad you like 🙂
It sounds as evocative as it looks. On the list for the next visit to NE Scotland!
I recommend it!
Wow! This is absolutely stunning!
It is a pretty phenomenal scene.
Stunning.
Wow what an amazing place to visit! Great photos, I love them 🙂
It really is amazing.
Stunning photos, thanks for sharing!
Glad you like 🙂
That view reminds me of the bluffs in Poldark… such awe-inspiring scenery!
I’m sure he could ride round those cliffs, no bother 😀
Completely stunning – thank you. My family is from the south west of Scotland, but I clearly need to explore further afield next time I’m up!
There are some great places to visit up here.
WOW!
Looks absolutely gorgeous. Would love to go there.
I hope you get the chance!
That post was unique! Astonishing views and wonderful comments. Feel homesick!
It is a unique place.
Dunnottar Castle was our favorite!
🙂
Love Dunnottar Castle! The Whig’s Vault where the imprisoned Covenanteers were left to rot was overwhelming. I imagined being imprisoned with them. It was something I will never forget. I was there in April, 2005 but didn’t see Charles’ II bedroom. So glad to see a great picture of it. Nice shot!
The history of that room is terrible; I didn’t read it until I was on my way out.
It certainly is terrible. I did realize or perhaps I have forgotten that this happened during Charles II reign. Can you imagine living above what was taking place below. Whoa!
What a stunning, and strategic, place to build a castle. 😀 … I go forth now to google-fu, and learn more. 🙂
Fascinating stuff!
The first picture especially is stunning! I’ll have to get back to Scotland just to see Dunnottar!
Worth it!
Amazing! Gorgeous! Wish I were standing there right now. Thanks for sharing.
I’m glad you like the post 🙂
Love this post Thanks for sharing. By the way. Have you read any of Elizabeth Chadwick’s books. She is an Historian and writes about all the periods in England and their Kings and Queens with a touch of Romance of course, but very well researched. I have read most of her books and can’t put them down. Looking forward to your next post.
I’ve not read any of her books; will have to look into them.
I think you will enjoy them. She has a blog. Elizabeth Chadwick.com
Thank you 🙂
Incredible, especially that first picture!
It is iconic, that view.
Just awesome!!
Loved visiting there. So dramatic and gorgeous!
Good description 🙂
looks wonderful, thanks for sharing!
Glad you like 🙂
Thank you for this, had hoped to visit Dunnottar Castle when I was in Scotland but sadly couldn’t make it. On the list for next time.
I’m sure you’ll enjoy it when you get there 🙂
Wonderful pictures of this fabulous castle, Ailish.
It’s so photogenic!
It’s breathtaking, if only those walls could talk 🙂
Indeed!
Every time I see one of your castle posts come across my email and read about the history, I’m reminded of just what a young country the US is.
I think you have some castles too? Not as old as this one though…
I’ve visited a castle in New Hampshire and one in Massachusetts. Both were built in the early 20th century by castle history buffs.
They must be interesting places. Someone locally here has recently constructed a new castle built to 16th century specifications.
Yes, they are. Hammond Castle in Gloucester, Massachusetts was built to authentic castle specifications (albeit from different eras), while Castle-in-the-Clouds in Moultenborough, New Hampshire was more castle-inspired.
They sound interesting!
Beautiful Pics. Wish I get to visit Scotland someday
I hope you get the chance!
It looks a wonderful place with stunning views!
The views are quite mesmerising.
Wow! that looks a fantastic place!
It really is.
These are stunning
Such a great place for photography!
Nice! Esp liked the window silhouette with the raised arms!
I just loved that sea view 🙂
I was drawn to that one as well!
Nicely done on a remote place:)
Also welcome to visit mine – thanks:
https://etravelersclub.wordpress.com/2019/09/11/countdown-to-incentive-travel-conference-meeting-asia-itcma-corporate-travel-world-ctw-bangkok-24-26-september-2019/
Fascinating!
Lovely post, Ailish. Being a largely Scottish girl, I avidly read anything to do with Scotland. My family is part of the Gordon clan in the Huntly area, though my direct ancestor’s estate was in the southwest corner, before he lost it somehow. Thanks for following my blog. I’ll follow yours and order your book. Good luck with it.
I live not too far from Huntly. The castle features in my snowy castle post here: https://ailishsinclair.com/2019/02/castles-in-the-snow/ And thank you 🙂
Amazing photography and descriptions. You really have the ”eye” for photography. Loved the composition of both your photos and your words. I’d like to see these or other photos with higher image definition. It would be nice.
Tricky for me to do with our slow rural internet. I tend to use my phone photos for online things.
Beautiful Pictures, Breathtaking!!
Thank you 🙂
wonderful pics, I just loved it
Thank you 🙂
My favorite Scottish Castle. It was so foggy there were no spectacular views of the sea. Your photos are stunning. Thank you for showing me what we missed.
It must have been quite atmospheric in the mist though…
It was very magical and mystical.
One of my favourite castles. Come to think of it all the best castles have sea view!
The sea does add a magical aspect somehow.
Thank you, for these wonderful pictures. x
I’m glad you like them 🙂
What a beautiful place and photos. Thanks for sharing.
I’m glad you enjoyed them 🙂
An interesting post, Ailish. Thanks for stopping by my blog and following. 🙂 — Suzanne
You’re welcome 🙂
I was in Northern Ireland in 2009. It was my first visit to this stunning country. I absolutely love Dunnotar Castle!
It is a wonderful place!
Breathtaking views. I could stare at the sea all day long.
Yes, it is quite breathtaking there.
I lived in Scotland for 3 years. Dunnattar was one of our favorite places to visit. Each stone tells a story. I left my heart in Scotland and trying to get back there for a nice visit
I hope you manage to get back 🙂
Such beautiful doorways to the past, and sometimes you let us see a bit of the fright as well.
🙂
Those do appear to be good views.
They really are 🙂
So much history that rests there; amazing to realize that the attack you describe happened over 700 years ago… yet the ruins still stand and tell the tale.
Oh, and the ocean is stunningly beautiful. I’d love to visit there someday.
It is a great place to visit; I hope you get the chance.
Looks lovely out there. And good pics!
It is lovely 🙂 And, thank you!
You’re welcome ☺️
I LOVE this castle. Used to visit often when I was wee. The history is tremdnous. Dunottar IS a castle in the true sense of the word. Thank you for the lovely post.
It is an amazing castle. I’m glad you liked the post.
it is. I still have an old guide book and pics taken–black and white ones– sitting on the castle well wall, also of Dunottar itself on the approach. Truly is quite a place. It is probably my fav Scottish castle.
Stunning beyond words! I can almost feel the ambience…
I’m glad you enjoyed the post 🙂